/ Cybersecurity as Discipline /
Cybersecurity in Digital Signage Isn't a Feature You Bolt On. It's a 20-Year Discipline.
On 29 April 2026, a logic bug in the Linux kernel — undetected for nine years — was published as CVE-2026-31431 with a CVSS score of 7.8. Every major Linux distribution since 2017 was affected. Three days later the AVIXA Digital Signage Power Hour debated SoC versus external players as if cybersecurity were a tier of features. It is not. It is a discipline you have either been practising for two decades, or you are about to discover at the worst possible time.

The AVIXA panel made cybersecurity the central question of the digital signage decade. The regional context made it concrete.
On 5 May 2026, the AVIXA Digital Signage Power Hour brought together Florian Rotberg of invidis with Eric Oliver (Poppulo), Joe Whitesides (AVI-SPL), and Nita Odera (Blue Rhine Industries) to debate System-on-Chip displays versus external media players. The technical question was framed in capability terms — fragmented operating systems, browser engines, processing power, sensor integration. But the security thread ran through every section, and three findings stood out clearly enough that they ought to change buying behaviour:
- Cyber-insurance underwriters are starting to refuse fleets running stale browser engines — typical SoC vintages of v50–v70 against a modern v150 — because the CVE distance is no longer defensible.
- Joe Whitesides' layered-vulnerability model — physical access, local network, user permissions, operating system — applies to every networked display. SoC versus external is not the main lever; the operating system, its patch cadence, and its installable-code surface are.
- Nita Odera's regional reality: actual cyber and physical attacks tied to regional conflict, including AWS-confirmed drone damage to three data centres with ~6-month recovery, plus on-premises mandates from GCC government and semi-government bodies.
Three days later, on 8 May, invidis published its market piece on the price doubling, the supply-chain disruption, and the fact that the cheap tier of digital signage hardware — already shaky on security — has stopped being cheap. The companion article on this site, Digital Signage Is No Longer a Purchase, It's an Investment, treats the economics of that change. This article treats the security side.
CVE-2026-31431 "Copy Fail" — Nine Years in the Linux Kernel, Found in an Hour with AI
On 29 April 2026, security researchers published CVE-2026-31431, nicknamed "Copy Fail": a logic bug in the Linux kernel's algif_aead module — the AF_ALG socket interface that exposes the kernel's userspace cryptographic API. CVSS score: 7.8 (High). The exploit fits in 732 bytes of Python, edits a setuid binary, and gives an unprivileged local user a root shell. The flaw was discovered through an AI-assisted process in approximately one hour.
CVSS score (High)
In mainline kernel undetected (since 2017)
To find with AI assistance
Major Linux distros affected
Affected: Ubuntu, RHEL, SUSE, Amazon Linux, Debian, Fedora, Arch — and the long tail of derivatives. If your digital signage CMS, content stack, or external media player runs on top of a general-purpose Linux distribution, your fleet inherited this CVE the day the kernel patch hit upstream. Patching it is a fleet-wide operation: kernel update, reboot, regression test, schedule a maintenance window across thousands of endpoints, and accept that the next CVE in this class is already being written.
Architectural footnote
SpinetiX DSOS is not exploitable. CVE-2026-31431 requires an unprivileged local user with the ability to execute arbitrary native code — the precondition for the privilege escalation. DSOS does not provide that surface. There is no shell. There is no SSH. There is no interactive login. There is no package manager and no path through which a remote actor can introduce executable code. (DSOS does use Linux service UIDs internally — to separate privileges between network-facing daemons — and Control Center has its own authentication credentials. Neither maps to a login session and neither accepts remote code.) The vulnerability surface assumed by Copy Fail does not exist on a properly-architected purpose-built signage firmware. The kernel flaw can be entirely real and architecturally inert at the same time. That is what twenty years of secure-by-design buys you.
And consider what Copy Fail demonstrates beyond its own CVE record: a class of bug sat in mainline Linux for nine years, used by tens of millions of systems, and was found in an hour once an AI was pointed at the right corner of the kernel. The next nine-year-old bug is already there. Cybersecurity is a moving target. The only durable defence is an architecture that gives the moving target nowhere to land.
DSOS Impact Assessment — Two CVEs, One Architecture
Media La Vista tracks every Linux-kernel CVE with potential reach into the deployed estate. For the two disclosures currently in flight — CVE-2026-31431 "Copy Fail" and CVE-2026-43284 "Dirty Frag" — SpinetiX engineering has confirmed the impact analysis, and neither is exploitable on a properly-deployed DSOS fleet. The reason is not luck; it is the firmware architecture. Expand each row for the engineering reasoning, the affected hardware lines, and the patch posture.
CVE-2026-31431 Copy Fail — kernel AF_ALG flaw, architecturally inert on DSOS
Models technically affected
All DSOS hardware except HMP3xx and DiVA
The vulnerable kernel module is present in the firmware on those models; the patched kernel is being rolled into the next minor firmware release.
Exploitability in practice
Non-critical — no usable local-code path
Copy Fail is a local privilege escalation. It requires the attacker to already be running native code on the player. DSOS exposes no shell, no SSH, no interactive login, and no installable software — so the precondition is structurally absent. (Internal Linux service UIDs and Control Center auth credentials exist, but none of them maps to a remote-execution surface.)
Where an attacker would normally chain it. Copy Fail is a privilege-escalation primitive; to matter, it must be coupled with a remote-code-execution vulnerability that hands the attacker local code execution first. On a general-purpose Linux distribution, that RCE pipeline runs through services, package managers, installed daemons, or browsers. On DSOS the realistic injection surfaces are the two JavaScript runtimes that execute content: V8 inside the HTML renderer (Chromium Embedded Framework — CEF) and the JavaScript engine in the SVG renderer (where Elementi project JavaScript runs). Depending on the content-distribution model either of these can be exposed to untrusted JavaScript. Neither engine can reach the AF_ALG kernel API used by the exploit, and the cryptographic primitives DSOS uses do not route through the kernel crypto API. Chromium itself, V8, and BoringSSL are unaffected. The chain therefore terminates before it begins.
Remediation cadence. The patched kernel is rolled into the next minor DSOS firmware release across the affected models. Because the fleet is not exploitable in the interim, this proceeds as an ordinary release cycle rather than an emergency rollout — the kind of patch posture that secure-by-design architecture is designed to permit.
CVE-2026-43284 Dirty Frag — vulnerable kernel modules never compiled into DSOS
DSOS impact
Not affected — code path not present
The kernel modules that carry the Dirty Frag flaw are not part of the DSOS kernel build. Vulnerable code that does not exist on the device cannot be exploited on the device.
Why a minimal kernel build matters. A general-purpose Linux distribution compiles in dozens of modules so that any host might use any device or filesystem later. A purpose-built signage firmware compiles only what the player actually needs to run signage. That single architectural decision — taken twenty years ago and maintained release after release — is the reason Dirty Frag costs DSOS-based deployments zero patch operations. It is also the reason a long tail of Linux-kernel CVEs that land in modules DSOS does not include are silently non-applicable.
Patch posture. Because the vulnerable code is absent rather than mitigated, there is nothing to ship. Procurement and security teams asking the standard CVE question ("are you patched yet?") can record this disclosure as architecturally inapplicable for their SpinetiX-based estate.
Source: SpinetiX Support Wiki — Linux Copy Fail and Dirty Frag vulnerabilities. Cross-verified by Media La Vista against the deployed estate. When SpinetiX publishes a DSOS-relevant CVE advisory, the impact analysis is reflected here.
The Hidden Assumption in "SoC vs External Player"
The AVIXA Power Hour framed the buyer's choice as binary: the System-on-Chip player built into the commercial display (now ~7 of 10 deployed signage screens worldwide), or an external media player running a general-purpose OS — Linux-derived, Windows-based, or Chrome OS. The framing is incomplete in the way that matters most for security.
Both sides of that binary share a property: they run general-purpose operating systems behind a signage skin. SoC displays ship Tizen, webOS, or one of many Android variants. Generic external players run general-purpose Linux derivatives, Windows IoT, or Chrome OS. Each one inherits the entire CVE pipeline of its underlying platform — including, for Linux-based devices in 2026, the freshly-disclosed Copy Fail.
The third option, missing from that binary, is a purpose-built secure player on hardened firmware: SpinetiX DSOS on industrial-grade SpinetiX hardware. This is the option that carries the architectural virtues of SoC — low power draw, low memory exposure, focused attack surface — without inheriting the SoC limits. There is no fragmented OS to track. There is no browser engine to age out. There is no patch backlog measured in years. There is no general-purpose runtime to host an exploit.
This option is not new. It has been the option since 2007. The market debate has finally caught up to a specification SpinetiX has shipped for two decades.
Option A
SoC built into the display
- ✓ Cleanest install, lowest BOM
- ✓ Low power draw
- ✗ Fragmented OS (Tizen / webOS / Android variants)
- ✗ Browser engines often stuck at v50–v70
- ✗ Update cadence ~24 months — "unacceptable" per AVIXA panel
- ✗ Cyber-insurance starting to refuse
Option B
Generic external player
- ✓ More CPU/GPU than SoC
- ✓ Better video-wall and complex-layout support
- ✗ Inherits full CVE surface of underlying OS
- ✗ Copy Fail and similar Linux/Windows kernel CVEs land here
- ✗ Browser-based content stack carries Chromium CVE pipeline
- ✗ Patch operations require fleet-wide reboots
Option C — the third option
Purpose-built signage firmware
- ✓ No shell, no SSH, no installable software
- ✓ No browser engine baseline to age out
- ✓ Hardened cryptographic stack on a contractual patch cadence
- ✓ Industrial hardware, <1% failure over 10 years
- ✓ Local-first content — works without cloud
- ✓ 20-year track record. SpinetiX DSOS, since 2007.
What Twenty Years of Discipline Actually Buys You
"Secure by design" is now a phrase on every brochure. The honest test is what the architecture delivers under stress — when a CVE drops, when an underwriter audits, when a regulator asks for evidence, when the cloud goes dark. Five things, each a direct response to the 2026 threat environment.
A Current Cryptographic Stack — That Passes Underwriting Today
Cyber-insurance underwriters are no longer treating browser-engine vintage as cosmetic. The AVIXA panel reported that fleets running Chromium v50–v70 are starting to fail underwriting checks against modern v150-class engines. The remediation is not a patch — these engines often cannot be patched in place — but a platform change. SpinetiX DSOS does not depend on a browser engine for its security posture. The cryptographic surface is part of the firmware, on a contractual patch cadence, signed at the vendor. There is no class of underwriter refusal that applies to "your browser engine is too old," because there is no exposed browser engine.
A Patch Cadence Measured in Weeks, Not Years
The AVIXA Power Hour described 24-month signage SoC update cycles as "unacceptable" — and praised Microsoft's MDAP push toward mandatory quarterly Android security patches as the new bar. SpinetiX has shipped against a faster cadence than that for the entire history of the platform. DSOS firmware lifecycle is contractual, signed, and tracked across compatible hardware generations. When Copy Fail-class disclosures land, the fleet response is not a multi-week scheduling exercise across thousands of endpoints — it is a controlled firmware rollout with a known SLA. This is what "discipline" looks like operationally.
Architecture That Survives Without the Cloud
Nita Odera's panel contribution was concrete: regional conflict produced real attacks, including AWS-confirmed drone damage to three data centres with a recovery window of approximately six months. Cloud-native signage architectures across the affected industries went dark. SpinetiX players store all content locally and accept emergency-content overrides over LAN even when the WAN is gone — see When the Cloud Burns: Zero-Trust Digital Signage for the full architectural argument. For Middle East deployments, this is not theoretical. The AWS event was 2026 — recent enough that most insurance renewals are still being repriced against it.
Audit Trails, RBAC, 802.1X, VLAN-Aware Behaviour — Designed In, Not Bolted On
The five layers of the SpinetiX security architecture — covered in detail at /security/ — are integrated, not sequential. Identity, transport, content, operating system, and audit are designed as a single architecture, not assembled from off-the-shelf parts. When a cybersecurity audit asks for evidence — a regulator under UAE PDPL, an underwriter under cyber-insurance, an internal CISO mapping ISO 27001 controls — the artefacts already exist, signed and dated. They do not need to be assembled from a configuration in retrospect.
Hardware That Doesn't Change Unpredictably
White-label SoC and SoC-display OEMs swap silicon families on quarterly cycles. The "enterprise Android signage box" you bought last year is often a different motherboard, with a different chipset, behind the same model name today. From a security-engineering standpoint that is intolerable: every silicon change is a re-validation event. SpinetiX has shipped four compatible hardware generations across eighteen years; the security surface is documented and stable. The vendor knows what is in the box because the vendor specified, manufactured, and certified what is in the box.
AI in Signage: Switchable, Contained — Not Embedded Liability
The AVIXA panel was direct on AI as well. Eric Oliver of Poppulo confirmed ISO 42001 certification for their AI workloads — the first signage CMS to hold it — and described the market shift away from large general-purpose models toward small, brand-safe language models running under Bring-Your-Own-AI patterns and MCP server isolation. The customer requirement was clear: AI must be switchable on and off, and enterprises with their own certified AI stacks refuse uncontrollable embedded AI on their signage.
This pattern matches SpinetiX's architectural separation natively. The player runs hardened firmware. AI integrations are explicit and occur in the content authoring layer (Elementi, Arya, HUB, customer-side automation) rather than baked into the firmware. The same audit that fails stale Chromium also fails uncontrolled embedded AI; SpinetiX passes both, because the architecture was always layered.
One adjacent panel finding is worth quoting: AI-generated "pretty pictures" are increasingly spotted by younger audiences as inauthentic, and damage brand trust when they are. The signage layer cannot solve content authenticity by itself, but it can ensure that the authoring tools remain in the hands of humans who own the brand voice. SpinetiX's data-driven content engine with 250 widget-constructors is built for human-led content with selectively-applied AI assistance, not for autoplay templates.
Compliance is a security layer
Dubai Law No. (2) of 2026 — The Test Case
Cybersecurity is layered. So is compliance. Dubai Law No. (2) of 2026, in effect from June 2026, requires every commercial venue in Dubai to operate emergency safety signage that fires within seconds, in Arabic and English, with location-specific evacuation routes — even when the internet is unavailable. Fines reach AED 2 million per non-compliance event.
Read the requirements as a security spec and they line up precisely with the discipline this article is about. Local-first content (resilience). API-triggered emergency overrides (controlled integration). Native multilingual rendering (no third-party plugins to fail-open). Signed firmware (auditable identity). Regional Tier-1 support (named accountability). The Law treats signage as critical infrastructure and prices the failure mode accordingly. A budget SoC stack with a stale browser engine and a vendor who patches twice a decade cannot pass it. The cybersecurity argument and the compliance argument converge on the same architecture.
Education, healthcare, banking, and transport carry parallel sectoral mandates of their own. The AED 2M figure is concrete; the broader pattern is a regulatory floor rising under every regulated venue.
Where SoC Is Fine, Honestly
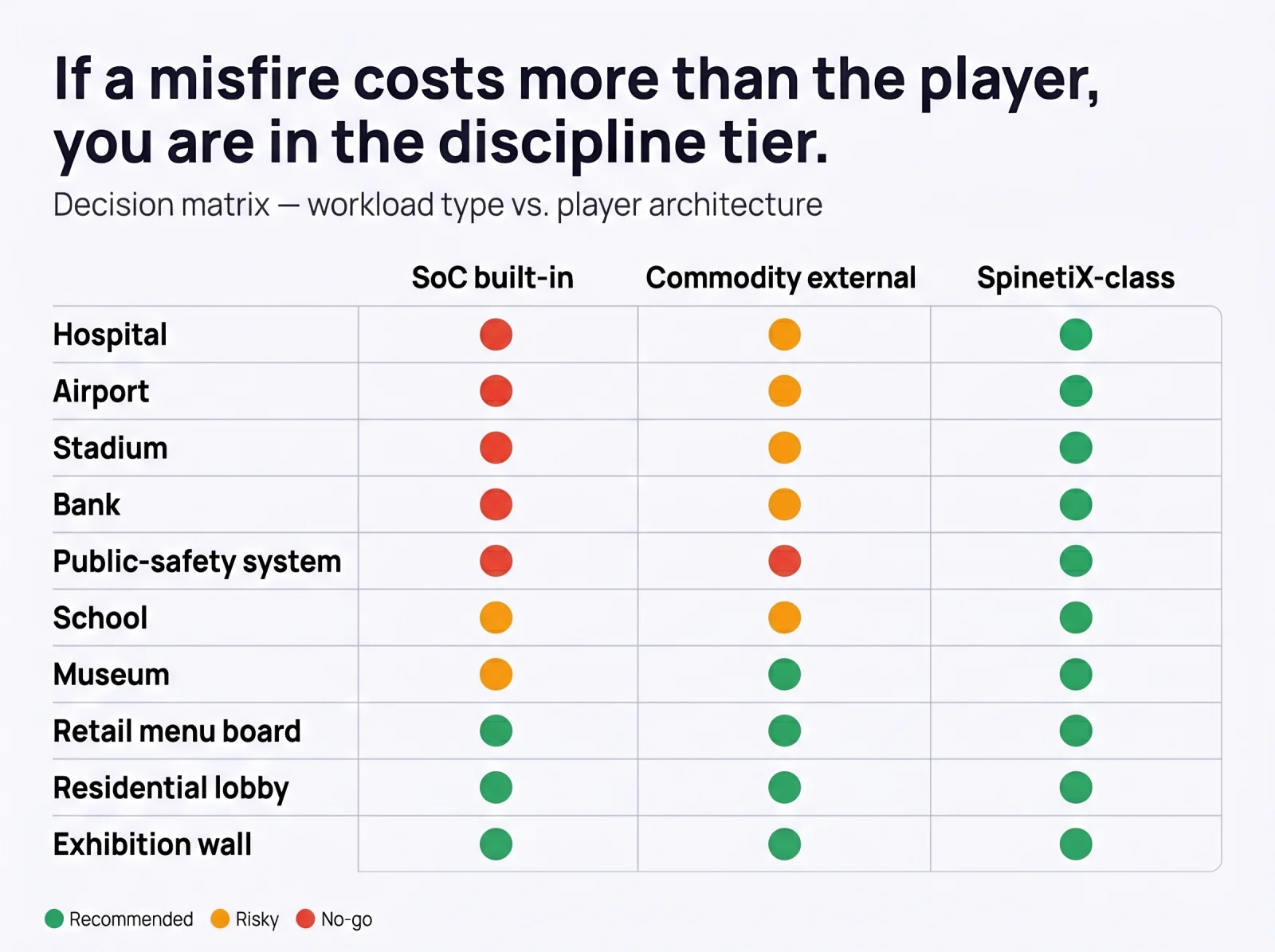
This article is not against SoC. SoC is a perfectly rational economic choice for low-stakes deployments where a misfire costs a refund or a customer-service call: residential community lobbies, simple retail menu boards, internal corporate welcome screens, exhibition walls bound to a single event. We deploy SoC ourselves where the use case justifies it.
The dividing line is the misfire cost. Once a screen carries a regulatory obligation, a life-safety role, a financial-decision context, or a reputation-bound customer experience, the architecture has to match the consequence. That is the line the AVIXA panel circled around. The decision rule below makes it explicit.
No Buy-and-Kick-Off — Especially in Cybersecurity
Cybersecurity is not a one-time procurement. It is a moving target. CVE-2026-31431 demonstrates that with a flaw nine years old in mainline Linux, found in an hour with AI assistance, on a CVSS 7.8 score. The next bug of that class is already being written.
A vendor and a regional partner who disappear after the PO is closed leave the customer to track that moving target alone. This does not work. The investment-grade architecture of 2026 needs an investment-grade operational model behind it: contractual patch cadence, named in-region engineers, an academy that trains the operator's staff, integration support for regulatory changes, and an accountability chain that survives turnover on either side.
Media La Vista has run that model as the regional Master Distributor for SpinetiX since 2007 — Tier-1, Tier-2, Tier-3 support across 18+ Middle East and CIS countries, the ME Academy for partner training and certification, and a 14-service operational scope from pre-sales through end-of-life. Cybersecurity is not a product we sell on top. It is the discipline that the rest of the work happens inside.
Once You Decide to Invest, Invest With the Partner Who Built the Discipline Before the Regulation Required It
Copy Fail will not be the last nine-year-old bug found in an hour by an AI. Cyber-insurance refusal letters will not stop landing on procurement desks. Dubai Law No. (2) of 2026 will be followed by other regimes in other regulated venues. The threat environment is moving — and it is moving in one direction.
The market is now asking, loudly, for what SpinetiX has shipped quietly for twenty years: hardened firmware, no general-purpose attack surface, controlled patch cadence, regional accountability, audit-ready compliance evidence. We do not have to catch up. We have to make sure that you do not have to.
If you are committing real money to a signage rollout in 2026 — and after the price doubling, every signage rollout commits real money — the architecture and the partner have to match the threat environment. The cybersecurity discipline is not a feature line on a tender. It is the precondition for the conversation.
Frequently Asked
What is CVE-2026-31431 "Copy Fail" and why does it matter for digital signage? +
What about CVE-2026-43284 "Dirty Frag" — is DSOS affected? +
Isn't "secure by design" just marketing language? +
What did Nita Odera at the AVIXA Power Hour say about Middle East cyber-risk? +
Why are cyber-insurance underwriters refusing fleets with stale browsers? +
What is the SoC vs external player debate, and what is the third option? +
How does this connect to Dubai Law No. (2) of 2026? +
If SoC is fine for some use cases, when is it the right call? +
Sources cited in this article
- AVIXA — Digital Signage Power Hour: "Optimizing Digital Signage — Media Players vs Built-In Apps," 5 May 2026. Panel: Florian Rotberg (invidis, host), Eric Oliver (Poppulo), Joe Whitesides (AVI-SPL), Nita Odera (Blue Rhine Industries). Watch on avixa.org →
- invidis Consulting — Florian Rotberg, "Media Player Prices: How AI and Geopolitics Are Hitting Digital Signage Hardware," 8 May 2026. Read on invidis.com →
- Microsoft Security Blog — "CVE-2026-31431: Copy Fail vulnerability enables Linux root privilege escalation across cloud environments," 1 May 2026. Microsoft advisory →
- CERT-EU — "High Vulnerability in the Linux Kernel (Copy Fail)," advisory 2026-005. CERT-EU advisory →
- Ubuntu / Canonical — "Fixes available for CVE-2026-31431 (Copy Fail) Linux Kernel Local Privilege Escalation Vulnerability." Ubuntu advisory →
Next step
Audit your signage estate against the 2026 threat environment.
We do a free architecture-and-security review for regulated and mission-critical estates: a one-call read of the existing fleet, a CVE-exposure score against general-purpose OS dependencies, a compliance-mapping check against UAE PDPL, NCA ECC, ISO 27001, and Dubai Law No. (2) of 2026, and a written note of what would need to change to make the deployment audit-ready.
Continue Reading
Digital Signage Is No Longer a Purchase. It's an Investment.
When the Cloud Burns: Zero-Trust Digital Signage
SpinetiX Security Architecture — Five Defense Layers
Dubai Law No. (2) of 2026 × SpinetiX: Emergency Infrastructure
Mission-Critical Media Infrastructure — Definition, Line, Architecture
Threat Model for Signage Networks
Or return to the Knowledge Center for the full library of architecture, security, and operations guidance.
